Quiz : How Well Do You Know About Advanced Networking?
(16).jpg)
.
Just how well do you know about advanced networking? Advanced Networks are independent practice associations or integrated delivery system organizations that have entered into SSP arrangements with at least one payer. Why not take this quiz and test your knowledge? Please make sure to read all the questions carefully. All the questions in the quiz are designed to make you think and test your knowledge. Interestingly, the quiz can help you learn new things about the concept. There is no time limit on the quiz, so you can take it as many times as you like. Have fun!
- 1.
Which port number is used by SMTP?
- A.
20
- B.
23
- C.
25
- D.
143
Correct Answer
C. 25Explanation
SMTP (Simple Mail Transfer Protocol) is a protocol used for sending emails. The port number 25 is specifically assigned to SMTP, allowing email clients and servers to communicate with each other. This port is used for establishing a connection between the sender and recipient's mail servers, enabling the transfer of email messages. Therefore, the correct answer is 25.Rate this question:
-
- 2.
End system use port numbers to select the proper applications. What is the lowest port number that can be dynamically assigned by the host system?
- A.
1
- B.
128
- C.
256
- D.
1024
Correct Answer
A. 1Explanation
The lowest port number that can be dynamically assigned by the host system is 1. Port numbers are used to identify specific applications or services running on an end system. The range of port numbers is from 0 to 65535, with the well-known ports (0-1023) reserved for specific protocols and services. Dynamic or ephemeral ports (also known as private ports) are assigned by the host system to client applications for temporary use. These ports typically start from 49152 and go up to 65535. However, the lowest possible dynamic port number is 1.Rate this question:
-
- 3.
During data transfer, what is the receiving host responsible for ? Choose two
- A.
Encapsulation
- B.
Bandwidth
- C.
Segmentation
- D.
Acknowledgement
- E.
Reassembly
Correct Answer(s)
D. Acknowledgement
E. ReassemblyExplanation
During data transfer, the receiving host is responsible for two tasks: acknowledgement and reassembly. Acknowledgement refers to the process of the receiving host sending a confirmation back to the sending host that the data has been received successfully. This ensures reliable communication and allows the sending host to know that the data reached its destination. Reassembly, on the other hand, involves the receiving host reconstructing the transmitted data from smaller segments or packets. This is necessary because data is often divided into smaller units for efficient transmission over a network, and the receiving host needs to put these pieces back together in the correct order to make sense of the data.Rate this question:
-
- 4.
Which of the following describes the operation of TCP window size?
- A.
Window size increases as all data transfers.
- B.
Window size is the TCP process used prepare data for transmission.
- C.
Window size is decreased if packets are lost.
- D.
Window size of 15 means that the next byte expected is byte number 15.
Correct Answer
C. Window size is decreased if packets are lost.Explanation
The TCP window size refers to the amount of data that can be sent without receiving an acknowledgment from the receiver. When packets are lost, the TCP window size is decreased to prevent further congestion and ensure reliable transmission. This allows the sender to adjust the rate at which data is sent based on the network conditions and the receiver's ability to handle the data. Therefore, the statement "Window size is decreased if packets are lost" accurately describes the operation of TCP window size.Rate this question:
-
- 5.
What is the purpose of TCP/UDP port numbers ?
- A.
To indicate the beginning of a three-way handshake
- B.
To reassemble the segments into the correct order
- C.
To identify the numbers of the data packets that can be sent without acknowledgment
- D.
To track the different conversations crossing the network at the same time
Correct Answer
D. To track the different conversations crossing the network at the same timeExplanation
TCP/UDP port numbers are used to track the different conversations crossing the network at the same time. Each conversation or communication session between two devices is assigned a unique port number, which allows the network to differentiate between multiple ongoing conversations. This ensures that the data packets from each conversation are correctly delivered to the intended recipient. By tracking the conversations using port numbers, the network can effectively manage and route the data packets to the correct destinations, enabling simultaneous communication between multiple devices on the network.Rate this question:
-
- 6.
There are ______ bits in an octet?
- A.
8
- B.
5
- C.
4
- D.
9
Correct Answer
A. 8Explanation
An octet is a sequence of 8 bits, therefore there are 8 bits in an octet. Each bit can have a value of either 0 or 1, and when combined in groups of 8, they form an octet. This is a standard unit of digital information in computing and telecommunication systems.Rate this question:
-
- 7.
Unicast is considered a one to one type of communication ?
- A.
True
- B.
False
Correct Answer
A. TrueExplanation
Unicast is indeed considered a one-to-one type of communication. In a unicast communication, data is sent from a single sender to a specific receiver. This means that the sender is targeting a specific recipient and the communication is exclusive between these two parties. Unlike multicast or broadcast communication, where data is sent to multiple recipients simultaneously, unicast ensures that the message is delivered to only one intended recipient. Therefore, the answer "True" is correct.Rate this question:
-
- 8.
What is the broadcast address for the network in which 192.168.242.5/20 is located?
- A.
192.168.251.251
- B.
192.168.250.250
- C.
192.168.255.255
Correct Answer
C. 192.168.255.255Explanation
The broadcast address is the highest possible address in a network and is used to send data to all devices on the network. In this case, the given IP address is 192.168.242.5 with a subnet mask of /20. This means that the network portion of the IP address is 192.168.240.0. Since the subnet mask is /20, the remaining bits in the IP address are all set to 1, resulting in a broadcast address of 192.168.255.255.Rate this question:
-
- 9.
What is the net ID for the network in which 192.168.242.5/20 is located?
- A.
192.168.241.1
- B.
192.168.240.0
- C.
192.168.242.2
Correct Answer
B. 192.168.240.0Explanation
The net ID for the network in which 192.168.242.5/20 is located is 192.168.240.0. This is because the given IP address has a subnet mask of /20, which means that the first 20 bits are used for the network ID. Therefore, the network ID is obtained by setting the last 12 bits of the given IP address to 0, resulting in 192.168.240.0.Rate this question:
-
- 10.
You are given the IP Address of 193.103.20.0 /24 and need 50 Subnets. How many hosts per network, and total networks do you get once subnetted.
- A.
20 Hosts and 50 Subnets
- B.
2 Hosts and 64 Subnets
- C.
4 Hosts and 50 Subnets
- D.
6 Hosts and 64 Subnets
Correct Answer
B. 2 Hosts and 64 SubnetsExplanation
193.103.20.0 Need 50 Networks
128 64 32 16 8 4 2 1
0 0 1 1 0 0 1 0 = 50 in binary
Need to borrow 6 bits for # of Networks
New Subnet Mask = 255.255.255.11111100 (252) or /30
^ Increment = 4
2^6 = # of Networks = 64
2^2-2 = # of Hosts per Network = 2
First 5 IP Ranges
193.103.20.0 - 193.103.20.3
20.4 – 20.7
20.8 – 20.11
20.12 – 20.15
20.16 – 20.19Rate this question:
-
- 11.
Subnet the Class B IP Address 130.13.0.0 into 500 Subnets. What is the new Subnet Mask and what is the Increment?
- A.
Subnet Mask 255.255.255.0 with an Increment of 2
- B.
Subnet Mask 255.255.255.192 with an Increment of 128
- C.
Subnet Mask 255.255.255.128 with an Increment of 128
- D.
Subnet Mask 255.255.255.128 with an Increment of 64
Correct Answer
C. Subnet Mask 255.255.255.128 with an Increment of 128Explanation
130.13.0.0 Need 500 Networks
128 64 32 16 8 4 2 1 . 128 64 32 16 8 4 2 1
0 0 0 0 0 0 0 1 . 1 1 1 1 0 1 0 0 = 500 in binary
Need to borrow 9 bits for # of Networks
New Subnet Mask = 255.255.11111111.10000000 (255.128) or /25
^ Increment = 128
2^9 = # of Networks = 512
2^7-2 = # of Hosts per Network = 126
First 5 IP Ranges
130.13.0.0 - 130.13.0.127
13.0.128 – 13.0.255
13.1.0 – 13.1.127
13.1.128 – 13.1.255
13.2.0 – 13.2.127Rate this question:
-
- 12.
Subnet the Address 150.20.0.0 into networks supporting 500 Hosts each. What is the New Subnet Mask and the IP Address Range of the first Network.
- A.
Subnet Mask 255.255.255.0, Range 150.20.0.0 - 150.20.0.255
- B.
Subnet Mask 255.255.0.0, Range 150.20.0.0 - 150.20.1.255
- C.
Subnet Mask 255.255.255.254, Range 150.20.0.0 - 150.20.255.255
- D.
Subnet Mask 255.255.254.0, Range 150.20.0.0 - 150.20.1.255
Correct Answer
D. Subnet Mask 255.255.254.0, Range 150.20.0.0 - 150.20.1.255Explanation
150.20.0.0 Need 500 Hosts per Network
128 64 32 16 8 4 2 1 . 128 64 32 16 8 4 2 1
0 0 0 0 0 0 0 1 . 1 1 1 1 0 1 0 0 = 500 in binary
Need to save 9 bits for # of Hosts
New Subnet Mask = 255.255.11111110.00000000 (254.0) or /23
^ Increment = 2 in the 3rd Octet
2^7 = # of Networks = 128
2^9-2 = # of Hosts per Network = 510
First 5 IP Ranges
150.20.0.0 - 150.20.1.255
20.2.0 – 20.3.255
20.4.0 – 20.5.255
20.6.0 – 20.7.255
20.8.0 – 20.9.255Rate this question:
-
- 13.
Refer to the exhibit. In this VLSM addressing scheme, what summary address would be sent from router A?
- A.
172.16.0.0/16
- B.
172.16.0.0/20
- C.
172.16.0.0/24
- D.
172.32.0.0/16
Correct Answer
A. 172.16.0.0/16Explanation
Router A receives 3 subnets: 172.16.64.0/18, 172.16.32.0/24 and 172.16.128.0/18.
All these 3 subnets have the same form of 172.16.x.x so our summarized subnet must be also in that form -> Only A, B or C is correct.
The smallest subnet mask of these 3 subnets is /18 so our summarized subnet must also have its subnet mask equal or smaller than /18.
-> Only answer A has these 2 conditions -> A is correct.Rate this question:
-
- 14.
Refer to the diagram. All hosts have connectivity with one another. Which statements describe the addressing scheme that is in use in the network? (Choose three)
- A.
The subnet mask in use is 255.255.255.192.
- B.
The LAN interface of the router is configured with one IP address.
- C.
The subnet mask in use is 255.255.255.128.
- D.
The IP address 172.16.1.25 can be assigned to hosts in VLAN1.
- E.
The LAN interface of the router is configured with multiple IP addresses.
Correct Answer(s)
C. The subnet mask in use is 255.255.255.128.
D. The IP address 172.16.1.25 can be assigned to hosts in VLAN1.
E. The LAN interface of the router is configured with multiple IP addresses.Explanation
VLAN 2 has 114 hosts so we need to leave 7 bits 0 for the host addresses (27 – 2 = 126 > 114). Notice that we are working with class B (both Host A and Host B belong to class B) and the default subnet mask of class B is /16 so we need to use 16 – 7 = 9 bits 1 for the sub-network mask, that means the subnet mask should be 255.255.255.128 -> B is correct.
By using above scheme, C is correct because the IP 172.16.1.25 belongs to the sub-network of VLAN 1 (172.16.1.0/25) and can be assigned to hosts in VLAN 1.
For communication between VLAN 1 and VLAN 2, the LAN interface of the router should be divided into multiple sub-interfaces with multiple IP addresses -> F is correct.Rate this question:
-
- 15.
Which layer of the hierarchical network design model is referred to as the high-speed backbone of the internetwork, where high availability and redundancy are critical?
- A.
Access Layer
- B.
Core Layer
- C.
Data Link Layer
- D.
Network Layer
Correct Answer
B. Core LayerExplanation
The core layer of the hierarchical network design model is referred to as the high-speed backbone of the internetwork, where high availability and redundancy are critical. This layer is responsible for providing fast and reliable connectivity between different parts of the network. It typically consists of high-performance routers and switches that can handle large amounts of traffic and ensure that data is efficiently routed between different network segments. The core layer is designed to be highly available and redundant to minimize downtime and ensure continuous network operation.Rate this question:
-
- 16.
Which layer of the hierarchical design model provides a means of connecting devices to the network and controlling which devices are allowed to communicate on the network?
- A.
Application
- B.
Access
- C.
Distribution
- D.
Core
Correct Answer
B. AccessExplanation
The access layer of the hierarchical design model provides a means of connecting devices to the network and controlling which devices are allowed to communicate on the network. This layer is responsible for handling user access and enforcing security policies. It also includes switches and access points that provide connectivity to end devices such as computers, printers, and phones. The access layer acts as a boundary between the end devices and the rest of the network, ensuring that only authorized devices can access the network and controlling the flow of traffic.Rate this question:
-
- 17.
Link aggregation should be implemented at which layer of the hierarchical network?
- A.
Core only
- B.
Distribution and core
- C.
Access and distribution
- D.
Access, distribution, and core
Correct Answer
D. Access, distribution, and coreExplanation
Link aggregation should be implemented at the access, distribution, and core layers of the hierarchical network. This is because link aggregation, also known as link bundling or port trunking, allows multiple physical links to be combined into a single logical link. By implementing link aggregation at all three layers, the network can achieve increased bandwidth, improved redundancy, and better load balancing across multiple links. This helps in optimizing network performance and ensuring high availability of network resources throughout the entire hierarchical network.Rate this question:
-
- 18.
- A.
Scalability
- B.
Security
- C.
Redundancy
- D.
Maintainability
Correct Answer
C. RedundancyExplanation
Redundancy refers to the duplication of critical components or systems in order to ensure continued operation in the event of a failure. It is an important factor in maintaining system availability and minimizing downtime. By having redundant systems or backups in place, organizations can mitigate the risk of single points of failure and ensure that operations can continue even if one component fails. This helps to improve the overall reliability and resilience of the system.Rate this question:
-
- 19.
Which hierarchical design model layer controls the flow of network traffic using policies and delineates broadcast domains by performing routing functions between virtual LANs (VLANs)?
- A.
Application
- B.
Access
- C.
Distribution
- D.
Network
Correct Answer
C. DistributionExplanation
The distribution layer in a hierarchical design model controls the flow of network traffic using policies and performs routing functions between virtual LANs (VLANs). This layer helps to segment the network into different broadcast domains and provides connectivity between different access layer switches. It also acts as an aggregation point for multiple access layer switches and connects them to the core layer. By separating the traffic and enforcing policies, the distribution layer ensures efficient and secure communication within the network.Rate this question:
-
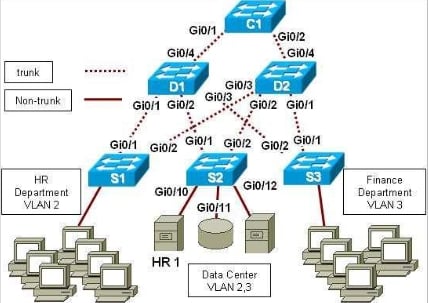
- 20.
- A.
Implement Layer 3 switching on S1 to reduce the packet processing load on D1 and D2. Install all security processing on S1 to reduce network traffic load.
- B.
Configure port security options on S1. Use Layer 3 access control features on D1 and D2 to limit access to the HR servers to just the HR subnet.
- C.
Move all HR assets out of the data center and connect them to S1. Use Layer 3 security functions on S1 to deny all traffic into and out of S1.
- D.
Perform all port access and Layer 3 security functions on C1.
Correct Answer
B. Configure port security options on S1. Use Layer 3 access control features on D1 and D2 to limit access to the HR servers to just the HR subnet. -
- 21.
Which two features are supported at all three levels of the Cisco three-layer hierarchical model? (Choose two.)
- A.
Power over Ethernet
- B.
Load balancing across redundant trunk links
- C.
Redundant components
- D.
Quality of Service
- E.
Link aggregation
Correct Answer(s)
A. Power over Ethernet
D. Quality of Service
E. Link aggregationExplanation
At all three levels of the Cisco three-layer hierarchical model, Power over Ethernet (PoE) is supported. PoE allows for the transmission of electrical power alongside data over Ethernet cables, eliminating the need for separate power cables. This feature is useful for powering devices such as IP phones, wireless access points, and IP cameras. Quality of Service (QoS) is also supported at all three levels. QoS allows for the prioritization and management of network traffic, ensuring that critical data, such as voice and video, receive higher priority and better performance. Link aggregation, which combines multiple physical links into a single logical link, is the third feature supported at all three levels. This improves bandwidth and provides redundancy.Rate this question:
-
- 22.
Configuring communication between devices on different VLANs requires the use of which layer of the OSI model?
- A.
Layer 1
- B.
Layer 2
- C.
Layer 3
- D.
Layer 4
- E.
Layer 5
Correct Answer
C. Layer 3Explanation
Configuring communication between devices on different VLANs requires the use of Layer 3 of the OSI model. Layer 3, also known as the network layer, is responsible for logical addressing, routing, and forwarding of data packets between different networks. VLANs are virtual LANs that separate devices into different broadcast domains, and in order for devices on different VLANs to communicate, a Layer 3 device such as a router is needed to route the traffic between the VLANs.Rate this question:
-
- 23.
Which layer of the OSI model does an access layer LAN switch use to make a forwarding decision?
- A.
Layer 1
- B.
Layer 2
- C.
Layer 3
- D.
Layer 4
Correct Answer
B. Layer 2Explanation
An access layer LAN switch uses Layer 2 of the OSI model to make a forwarding decision. Layer 2, also known as the Data Link Layer, is responsible for the reliable transfer of data between network nodes over a physical link. It handles tasks such as framing, error detection, and flow control. In the case of an access layer switch, it uses Layer 2 information, such as MAC addresses, to determine the appropriate port to forward incoming data packets to their destination within the local network.Rate this question:
-
- 24.
What are three benefits of a hierarchical network model? (Choose three.)
- A.
Reduced contention for bandwidth
- B.
Reduced size of the physical layout
- C.
Increased fault tolerance of the network
- D.
Elimination of the need for layer three functionality
- E.
Simplification of management and troubleshooting
Correct Answer(s)
A. Reduced contention for bandwidth
C. Increased fault tolerance of the network
E. Simplification of management and troubleshootingExplanation
The hierarchical network model provides three main benefits. Firstly, it reduces contention for bandwidth by dividing the network into different layers or levels, ensuring that traffic is distributed efficiently and congestion is minimized. Secondly, it increases fault tolerance of the network by allowing for redundancy and multiple paths, ensuring that if one part of the network fails, the rest can still function. Lastly, it simplifies management and troubleshooting by organizing the network into distinct layers, making it easier to identify and resolve issues within specific areas rather than the entire network.Rate this question:
-
- 25.
Is the transport protocol that manages the individual conversations between web servers and web clients.
Correct Answer(s)
Transmission Control Protocol , TCPExplanation
TCP (Transmission Control Protocol) is the transport protocol that manages the individual conversations between web servers and web clients. TCP ensures reliable and ordered delivery of data packets over the internet. It establishes a connection between the sender and receiver, breaks the data into smaller packets, and ensures that they are received in the correct order. TCP also handles congestion control and flow control to optimize the data transfer process. Overall, TCP plays a crucial role in ensuring the smooth and efficient communication between web servers and clients.Rate this question:
- 26.
Is responsible for taking the formatted segments from TCP, encapsulating them into packets, assigning them the appropriate addresses, and delivering them across the best path to the destination host.
Correct Answer(s)
Internet Protocol, IPExplanation
The correct answer is Internet Protocol, IP. IP is responsible for taking the formatted segments from TCP, encapsulating them into packets, assigning them the appropriate addresses, and delivering them across the best path to the destination host. IP is a fundamental protocol in the internet protocol suite and is responsible for routing packets across networks. It ensures that packets are properly addressed and delivered to the intended destination.Rate this question:
- 27.
Consists of a radio transmitter capable of connecting end devices wirelessly
Correct Answer(s)
Wireless access pointExplanation
A wireless access point is a device that enables end devices to connect to a wireless network. It consists of a radio transmitter that can establish a wireless connection with these devices. This device acts as a bridge between the wired and wireless network, allowing devices to access the internet or other resources without the need for physical connections. Therefore, a wireless access point is the correct answer as it accurately describes a device with a radio transmitter capable of connecting end devices wirelessly.Rate this question:
- 28.
Secures outgoing traffic and restricts incoming traffic
Correct Answer(s)
Firewall applianceExplanation
A firewall appliance is a device that is used to secure a network by controlling and monitoring incoming and outgoing traffic. It acts as a barrier between the internal network and the external network, allowing only authorized traffic to pass through while blocking any unauthorized or potentially harmful traffic. By doing so, it helps protect the network from external threats and ensures that outgoing traffic is secure.Rate this question:
Quiz Review Timeline +
Our quizzes are rigorously reviewed, monitored and continuously updated by our expert board to maintain accuracy, relevance, and timeliness.
-
Current Version
-
Aug 19, 2023Quiz Edited by
ProProfs Editorial Team -
Mar 12, 2014Quiz Created by
Bongeagle
 Back to top
Back to top